This article is part of a series.
View all 6 parts
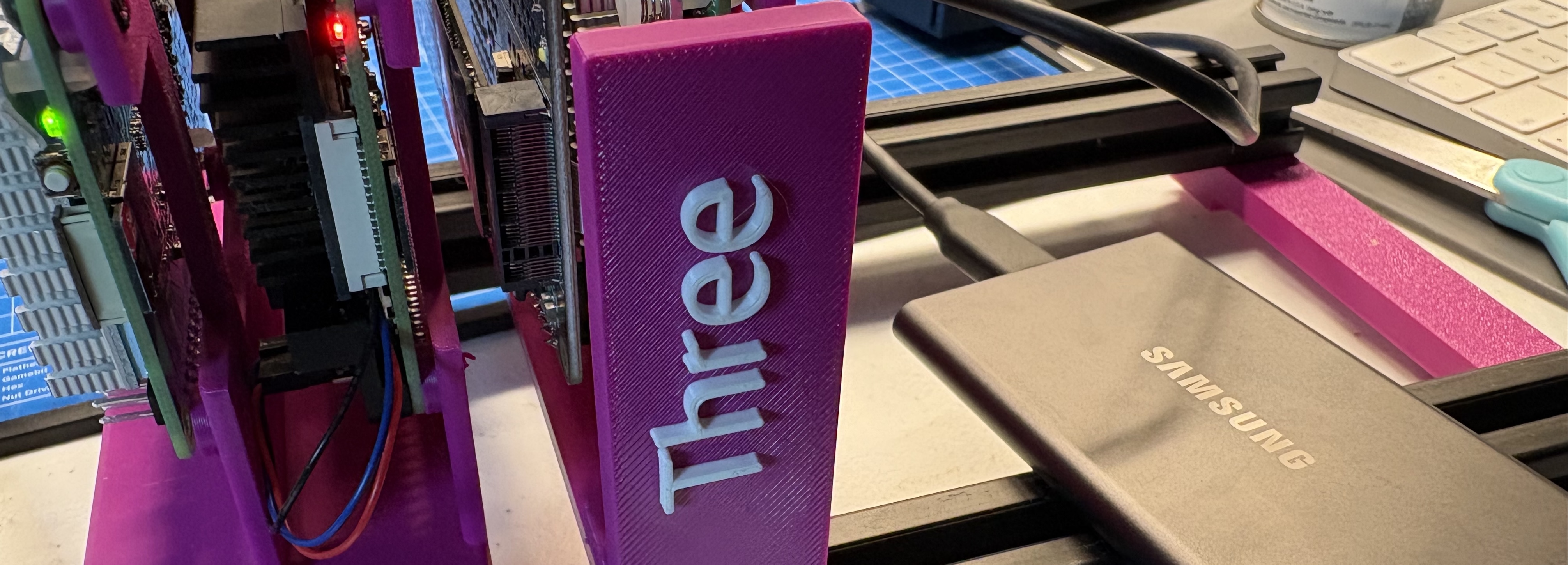
- Part 1 – Setting up a Raspberry Pi NAS
- Part 2 – This Article
- Part 3 – Securely Expose Your Raspberry Pi 5 with Cloudflare Tunnel
- Part 4 – Nginx Reverse Proxy on Raspberry Pi (Ubuntu Server)
- Part 5 – Add HTTPS to Your Raspberry Pi with Nginx and Cloudflare
- Part 6 – Switch from Cloudflare Origin Certificates to Let’s Encrypt on Raspberry Pi with Cloudflare Tunnel
This guide walks through exposing a
private PostgreSQL server
(e.g., running at
192.168.1.104
) to the internet securely using
Cloudflare Tunnel + Access
— ideal for containers, cloud VMs, and codex environments.
This method is production-capable, free (under 50 users), and requires no inbound ports or static IPs.
1. Prerequisites
-
Home PostgreSQL server on
192.168.1.104 -
Another home device (e.g., Pi, NUC) at
192.168.1.102runningcloudflared -
A domain managed by Cloudflare (e.g.,
lolzlab.com) - Remote client (Codex container, VM, laptop)
- Installed:
-
psql -
cloudflared
2. Configure the Cloudflare Tunnel (at home)
2.1 Install cloudflared on
192.168.1.102
curl -fsSL https://developers.cloudflare.com/cloudflare-one/connections/connect-apps/install/linux/ | bash
cloudflared tunnel login
2.2 Create a named tunnel
cloudflared tunnel create lolz_at_home
2.3 Create the config file:
# /etc/cloudflared/config.yml
tunnel: lolz_at_home
credentials-file: /root/.cloudflared/7503668c-xxxx.json
ingress:
- hostname: postgres.lolzlab.com
service: tcp://192.168.1.104:5432
- service: http_status:404
2.4 Create DNS route for the tunnel
cloudflared tunnel route dns lolz_at_home postgres.lolzlab.com
2.5 Enable and start the tunnel as a systemd service
sudo systemctl enable cloudflared
sudo systemctl start cloudflared
3. Enable Cloudflare Access for Postgres
- Go to Cloudflare Dashboard → Zero Trust → Access → Applications
- Click “Add an application” → “Self-hosted”
- Set:
-
Name:
Postgres -
Domain:
postgres.lolzlab.com4. Add a policy: -
Require login via GitHub, Google, or email 5. Save and deploy
This protects the TCP tunnel with identity auth (free for ≤ 50 users).
4. Set Up the Remote Client (e.g., Codex)
4.1 Install cloudflared (static binary method)
wget https://github.com/cloudflare/cloudflared/releases/latest/download/cloudflared-linux-amd64 -O /usr/local/bin/cloudflared
chmod +x /usr/local/bin/cloudflared
4.2 Authenticate with Cloudflare Access
cloudflared access login https://postgres.lolzlab.com
This stores an identity token in
~/.cloudflared
.
5. Connect to Postgres via Tunnel
5.1 Start the tunnel (TCP-only)
cloudflared access tcp --hostname postgres.lolzlab.com --url tcp://localhost:15432
You should see:
INF Start Websocket listener host=localhost:15432
5.2 Connect using psql
In another terminal:
PGPASSWORD='your_secure_password' psql -h localhost -p 15432 -U agent -d agent_sandbox
6. Optional: Background the Tunnel
nohup cloudflared access tcp --hostname postgres.lolzlab.com --url tcp://localhost:15432 > tunnel.log 2>&1 &
This frees your terminal while keeping the tunnel active.
7. Optional: Script It
Save this as
connect_postgres.sh
:
#!/bin/bash
cloudflared access tcp --hostname postgres.lolzlab.com --url tcp://localhost:15432 &
sleep 2
PGPASSWORD='your_secure_password' psql -h localhost -p 15432 -U agent -d agent_sandbox
Make it executable:
chmod +x connect_postgres.sh
8. FAQ and Tips
- Is this free? Yes. Tunnel + Access is free for up to 50 users.
- Can I use IPv6? Cloudflare tunnels prefer IPv6 outbound. If blocked, unset proxy or force IPv4.
- Is this secure? Yes. No open ports, TLS by default, and identity auth.
This method gives you enterprise-grade remote DB access for free — perfect for home labs, LLM agents, or containerized workflows.
Let me know if you’d like a
systemd
unit, Docker integration, or FastAPI wrapper!